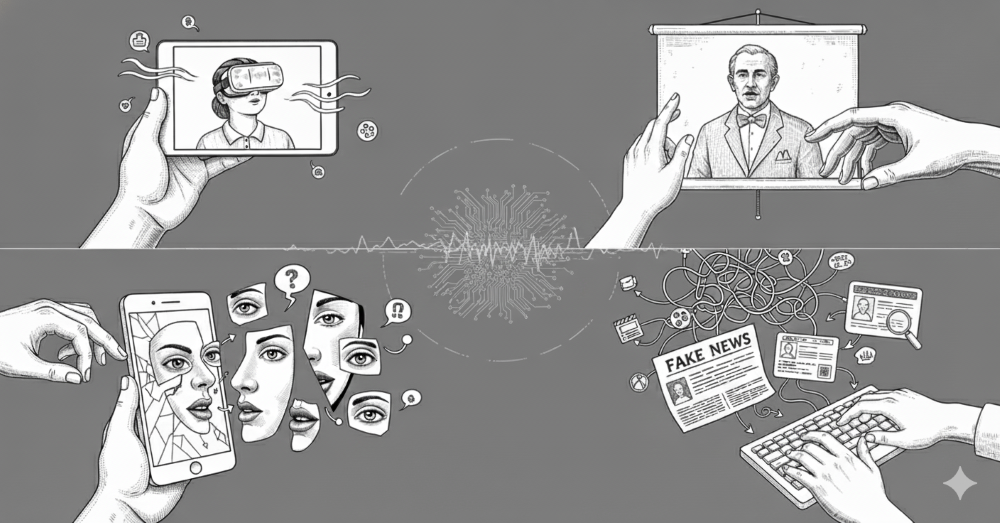
What if you couldn’t trust your own eyes or ears?
Welcome to the deepfake era, where artificial intelligence doesn’t just predict the future—it recreates the present. With a few lines of code and enough data, machines can now craft shockingly realistic videos, voices, and digital personas that mimic reality with near-perfect precision. It’s dazzling, it’s dangerous, and it’s blurring the line between fact and fabrication faster than we can blink.
But behind the digital magic lies a growing storm: challenges in detecting these fakes, protecting personal identities, and untangling the legal chaos of who owns what in this synthetic frontier. As generative AI races ahead, we’re not just facing a technological revolution. We’re staring down a truth crisis.
Deepfakes Demystified: When AI Plays Pretend
Deepfakes are artificial intelligence (AI)-generated or modified digital content that realistically imitates actual persons, events, or behaviours. These are mostly deep learning models. Deepfakes typically entail the manipulation of both audio and video. For example, someone may synthesise sounds of a politician saying something they have never said or replace the visage of a celebrity with their own.
Building the Illusion: How Deepfakes Are Made
Advanced machine learning methods, including Generative Adversarial Networks (GANs), Variational Autoencoders (VAEs), and more recently, diffusion models, are used in the creation of deepfakes.
GANs Unleashed: The Engine Behind Deepfakes
GANs operate through a competitive process between two neural networks:
• Generator: Tries to produce fake data that imitate real media.
• Discriminator: Attempts to distinguish real data from generated fakes.
The discriminator improves its capacity to spot differences as training goes on, while the generator becomes better at producing content that looks legitimate. The generator eventually creates hyper-realistic media with outputs that deceive even highly skilled discriminators.
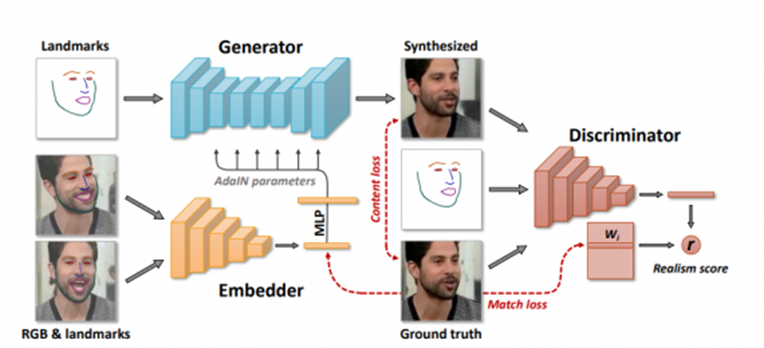
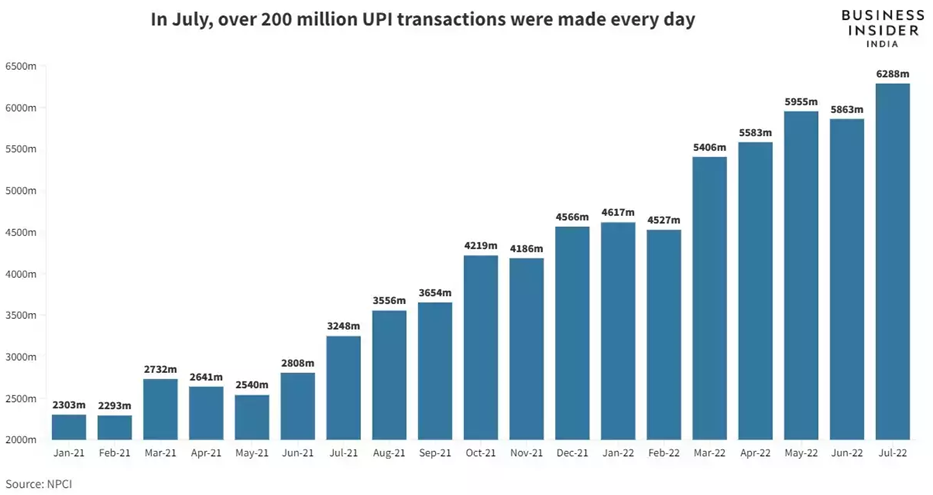
Figure 1: GAN architecture (https://neurohive.io/en/news/deepfake-videos-gan-sythesizes-a-video-from-a-single-photo/)
The Art of Deception: Deepfake Methods in Action
- Face Swapping: Replacing one person’s face in a video or image with another’s.
- Facial Reenactment: Mapping a person’s facial expressions onto another’s face in a video, making them appear to say or emote things they never have.
- Talking Faces: Generating mouth and face movements that precisely sync with arbitrary speech audio.
- Voice Cloning: Mimicking a person’s voice using small audio samples and generating new speech.
Large datasets of photos, films, and audio files are analysed for training in order to make these changes possible. Typically, the procedure entails identifying facial features and expressions in target clips, followed by pixel-by-pixel synthesis of replacement faces for every frame.
Power and Peril: Where Deepfakes Are Used and Misused
When Innovation Meets Intention:
- Entertainment and Cinema: Digital de-aging, resurrecting deceased actors, dubbing content into other languages without reshooting scenes.
- Accessibility: Providing personalized avatars for people unable to speak or move.
- Virtual Reality: Creating realistic digital personas.
The Flip Side of Progress:
- Disinformation: Fabricating speeches, news, or events to sway public opinion or manipulate elections.
- Fraud and Impersonation: Mimicking voices for scams or creating fake identification videos.
- Nonconsensual Content: Generating inappropriate images or videos.
Catching the Fakes: Why Spotting Deepfakes Isn’t Easy
Large datasets of photos, videos, and audio files are analysed for training in order to make these changes possible. Typically, the procedure includes recognising facial features and expressions in target clips, followed by pixel-by-pixel synthesis of replacement faces for every frame.
Tools of Truth: How Experts Detect the Digital Lies
- Visual Artifacts and Inconsistencies
- Unnatural facial movements: Odd blinking patterns, strange lip synchronization, or shifting facial features.
- Inconsistent lighting and shadows: Mismatches between facial lighting and the background.
- Blurring or artifacts: Especially at facial boundaries or in fast movements.
- Repetitive or exaggerated movements: Subtle, natural expressions are often hard for algorithms to correctly match.
- Audio-Visual Synchronization
- Analyzing whether the voice matches lip movement and ambient environment.
- Metadata Analysis
- Scrutinizing file metadata for unusual modifications or compression artifacts that suggest manipulation.
- AI and Neural Detection Tools
- Advanced machine learning tools trained to spot subtle pixel-level or spectral irregularities.
- Popular tools: Deepware Scanner, Microsoft Video Authenticator, Sensity AI, and Amber Authenticate.
- Digital Forensics
- Examining raw data for anomalies using sophisticated software or reverse image/video search.
Tech to the Rescue: Innovations in Deepfake Defense
- Integrated Multimodal Detection: Systems that evaluate both audio and visual streams for inconsistencies, often incorporating real-time analysis.
- Blockchain Authentication: Timestamping and verifying original content, so later manipulation is easier to detect.
- Continual Learning: Updating detection models as new deepfake generation tactics emerge.
- TC&C’s Deepfake Guard (2025 Solution) – One of the most advanced real-time detection platforms adopted by major corporations.
Rewriting Reality: The Patent That Signals a Deepfake Revolution
In 2022, Apple was granted a U.S. patent titled “Face Image Generation with Pose and Expression Control,” effectively formalizing its proprietary deepfake generation method.
What Does Apple’s Patent Cover?
- Generation from Reference Images: The patent describes using advanced neural networks to produce synthetic images of a human face based on a single reference image.
- Pose and Expression Control: Once the reference face is generated, the system can alter the subject’s expression (smiling, frowning, etc.) or pose (direction, angle), creating new synthetic but photo-realistic images or even animated sequences.
- GAN-Based Approach: Apple’s models use GANs, allowing a generator to create convincing fakes while a discriminator attempts to spot authenticity. The process iterates—leveraging the best aspects of current academic research—for ever-better results.
- Not Full Image Synthesis: According to available summaries, Apple’s system changes and alters existing photos but doesn’t generate entirely new faces from scratch.
- Potential Applications: The most immediate uses are likely in photo editing, digital avatars for virtual communications, entertainment effects, or accessibility features in iOS devices.
Legal Labyrinth: Deepfakes, Ethics, and Ownership
Apple’s move to patent deepfake technology raises issues beyond technical boundaries:
- Copyright and Originality: Digitally altered images may or may not qualify for copyright, especially if they infringe on original works.
- Privacy and Consent: Unauthorized manipulation of images for any purpose (creative or malicious) could lead to privacy violations or legal challenges.
- Regulation and Control: As big tech invests in synthetic media, legislation and ethical standards will determine how these innovations are used or abused.
- Personality and Publicity Rights: Courts increasingly recognize a person’s likeness, voice, and digital persona as protected.Celebrities and influencers are fighting back against deepfakes that damage reputation or monetize identity without consent.
- Trademark Law: Used to combat false endorsement or impersonation. Brands are pursuing takedowns of deepfakes that falsely associate synthesized appearances or voices with their name.
- Patent Trends: Companies, especially tech giants, are patenting both:
Generation tools (e.g., Apple and Adobe).
Detection and authentication platforms (e.g., Trust Stamp’s 2024 patent for biometric verification).
Laws vs. Lies: How the World Is Fighting Deepfakes (2025)
Recent Actions and Global Regulation Trends
- United States: Several states have enacted deepfake-specific laws focusing on issues such as election interference, nonconsensual sexual content, and AI-generated voice scams. Additionally, the Federal Communications Commission (FCC) implemented a ban on automated robocalls using AI-generated voices, a measure that came into effect during 2024-2025.
- European Union (EU): The EU is advancing its regulatory approach with the expansion of the AI Act. This legislation includes new requirements for labelling synthetic media and specific protections for individual likeness and privacy within digital content.
- India: Lawmakers have proposed draft regulations that would require clear labelling for all AI-generated digital content. These measures aim to enhance transparency and accountability around synthetic media.
- Australia: The country has passed the Criminal Code Amendment Act, which imposes penalties for unauthorized synthetic media that is created with the intention of deception or harm. This act is designed to deter the malicious use of deepfake technologies and protect individuals from synthetic media abuse.
These developments reflect a growing global consensus around the need for targeted legal frameworks that address the rapid rise of deepfake technology and synthetic media. Regulators are increasingly focused on promoting transparency, individual rights, and robust deterrents against abuse.
The Next Frontier: Balancing Innovation with Integrity
Because of the rapid improvements in both generation and detection, this field will be characterised by a continuous back and forth, with each development in deepfake artistry provoking a countermove from detection experts.
Key focus areas for future research and policy:
- Robust Detection at Scale: Ensuring detection tools work for both experts and the general public.
- Synthetic Media Disclosure: Automatically tagging or watermarking synthetic content.
- Ethical Oversight: Stronger frameworks to manage usage rights, consent, and privacy—especially as companies like Apple bring these technologies to mainstream consumers.
- Interdisciplinary Collaboration: Involving technologists, policymakers, ethicists, and creatives to shepherd the technology’s evolution in a positive direction.
Final Frame: Deepfakes, Responsibility, and the Future of Truth
Deepfake technology is the ultimate double-edged sword: equal parts marvel and menace. It opens doors to astonishing creativity, immersive storytelling, and next-gen virtual experiences. Yet lurking behind the innovation is a darker mirror that reflects the threats of deception, digital identity theft, and the erosion of trust in what we see and hear.
As deepfakes continue to blur the line between reality and illusion, one thing becomes crystal clear: truth is no longer self-evident; it must be protected. In this new era of synthetic media, intellectual property, privacy, and regulation aren’t just legal buzzwords. They are the frontlines of a battle for authenticity. The future won’t just be written in code. It will be shaped by our courage to question, legislate, and guard reality itself.